-
Secure Static Website Deployment
You don’t have to give up dynamic website features to get the benefits of a static website. Learn how migrating to a website powered by serverless hosting can reduce the attack surface of your site, increase site performance, and reduce recurring charges.
-
Preventing IP-based Drive-Bys in Apache
How many attacks is your webserver under from script kiddies and automated bots? If you’re allowing connections with IP addresses for host headers you’re servers are at greater risk than they need be. Learn how to filter out the noise and block requests that aren’t intended for your specific domain name.
-
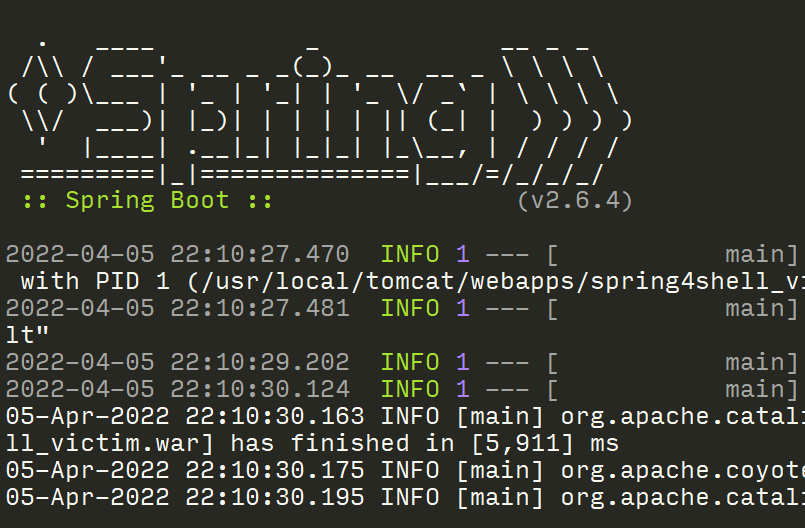
Security Camera Dynamic Analysis
The series on hacking IP cameras continues in this post, with the work moves on to the dynamic analysis phase.
Big Breaks Come From Small Fractures.
You might not know how at-risk your security posture is until somebody breaks in . . . and the consequences of a break in could be big. Don't let small fractures in your security protocols lead to a breach. We'll act like a hacker and confirm where you're most vulnerable. As your adversarial allies, we'll work with you to proactively protect your assets. Schedule a consultation with our Principal Security Consultant to discuss your project goals today.